Blind Spot
¥157.15
What can chess masters teach us about how humans become expertsWhy can't race car drivers explain decisions they've made behind the wheel?What does predicting the winner of a soccer match say about our ability to make the right choiceWhen we talk about experts, we typically have bought into the idea that they have all the answers. Now, in this groundbreaking book, Gordon Rugg exposes the surprising ways in which all people tend to make the same sorts of mistakes, regardless of what field they are in, how smart they are, or even their level of expertise. Focusing on why and how we make decisions, Rugg offers insight into what motivates us, how we fail to find the answers we are looking for, how we can learn to ask the essential questions, and more. Rugg has devoted his life to learning how experts solve problems. He gained international attention after arguing persuasively that the famous Voynich Manu* is a hoax. Now, he demonstrates his techniques in the Verifier Method, which can be applied to any seemingly unsolvable problem.Drawing on his personal odyssey in the field of human expertise, Rugg makes astute and entertaining conclusions about how and why we inevitably fail, and explains how to make better mistakes, work backward, and reengineer the ways we pursue success.
George Lucas's Blockbusting
¥168.37
A comprehensive look at 300 of the most financially and/or critically successful motion pictures of all time many made despite seemingly insurmountable economic, cultural, and political challenges set against the prevailing production, distribution, exhibition, marketing, and technology trends of each decade in movie business history.
If I Had a Hammer
¥106.61
Have fun, save money, and improve your home with these easy step-by-step projects Are you looking for a way to make your bathroom a little more beautifulOr maybe you'd like to give your tired furniture a face-lift, improve your home's air quality, or fix a toilet. No matter your DIY needs and no matter whether you're a DIY novice or expert, home improvement guru Andrea Ridout, host of the nationally syndicated radio show Ask Andrea, has ideas, expertise, and advice to share with you. If I Had a Hammer offers easy-to-follow instructions and illustrations designed to make home improvement simpler than ever. With a little help from Andrea, you'll be able to tackle repairs, painting and decorating, bathroom and kitchen remodeling, wood care for furniture and floors, and much more with projects that often take as little as an hour. Also, you can try a few of Andrea's energy-conserving projects that can dramatically improve your utility bill Andrea's projects are friendly on the environment and on your wallet! With If I Had a Hammer, you'll have the tools to keep your home functioning and looking as good as or even better than new.
Temptation of the Warrior
¥41.46
A new land, a new time . . .To protect his people from a great evil, Merrick Mac Lochlainn, newly crowned high chieftain of his clan, must travel forward in time nearly 1,000 years. But when he awakens in nineteenth-century England, he has no memory of his mission to save his race, nor can he recognize Jenny Keating, the spirited young beauty who calls herself his wife.A new love . . .Orphaned and on the run from a cruel headmaster, vulnerable and alone, Jenny never dreamed of being rescued by any man, much less a chivalrous and handsome warrior like Merrick. Drawn to his powerful physique and mysterious ways, she begins a dangerous deception and poses as his beloved. But her feelings of desire are all too real. Together they will battle a dark threat that jeopardizes their very lives, all the while tempting each other with a passion too powerful to resist.

Wild and Wicked in Scotland
¥42.03
Running wild . . .When Cassandra Sheridan agreed to an arranged marriage to the Earl of Hampstead, she never dreamed the cad wouldn't even bother to appear for their betrothal ball. It seems her intended cares more for gallivanting than meeting his bride-to-be! So Cassie decides to enjoy an adventure of her own and sets out across Scotland and meets a dashing stranger who has elevated dueling and deception to an art form.A dedicated spy on a mission, the Earl of Hampstead has more on his mind than a silly party. Now fate has thrown him together with a vivacious lady whom he must protect from harm, and whose sensuous beauty is proving most distracting. Worse still, Devlyn is horrified to discover she's the very woman he's engaged to marry!With their lives and reputations in equal peril, do they dare surrender to their irresistible desires?
The Renegades: Nick
¥42.03
The WomanFor the sake of her unborn child, Callie Sloane is willing to endure the hardships of this wild Western land but not her attraction to an untamed half-Cherokee renegade. She lost everything to love once before, and she's not making that mistake twice. While outlaw Nick Smith may be the most handsome man she's ever seen, he's also the most dangerous.The RenegadeNick watches in shock as a determined woman rides out of the dust clouds to plant her flag on his ancestral lands in the Great Oklahoma Land Run. The hardened loner vows not to help this stubborn female survive, but finds himself drawn time and again to protect her. And soon Nick has to protect himself from his own desire . . . for the innocent enchantress tempts him beyond anything he's ever known.
Confessions at Midnight
¥48.39
Carolyn Turner, Viscountess Wingate, is absolutely shocked by the Ladies Literary Society of London's latest selection. Memoirs of a Mistress is scandalously explicit and downright wicked . . . and it's stirring feelings within Carolyn that she hasn't felt . . . well, ever! She's sure that this steamy read is the only reason she's succumbing to the charms of notorious rogue Daniel Sutton, Lord Surbrooke. She couldn't possibly be falling for the rascal and his illicit caresses . . . or could she?The last thing Daniel wanted was to be shackled by marriage vows. He lusted after Carolyn, sure, but he never imagined that once he lured her to his bed he'd never want to let her go. Yet only when a murderer targets his beloved will he be spurred to confess his true love . . . and claim Carolyn as his bride.
Tallchief
¥48.39
A powerful classic repackaged love story featuring a Native American hero, touches of mysticism and suspense, and heartrending romance.Morgan Tallchief lives for the art he creates, but even that is haunted by the loss of the only woman he will ever love. When Kathleen Ryder mysteriously re-enters his life, the achingly sweet hunger that bound them together in the past returns as well.

The Eldercare Handbook
¥101.00
In this comprehensive and accessible guide, long-term care expert Stella Henry helps readers navigate the daunting logistics and powerful emotions of making care decisions for an elderly parent or loved one. Drawing from her 36 years as a registered nurse and a nursing home administrator, as well as her experience caring for both her parents (both of whom suffered the ravages of Alzheimer's disease), Henry tackles all the tough issues: spotting the warning signs of dementia, redefining sibling roles, doing a walk-through at an assisted living facility or nursing home, making the move, and coping with "take me home!" demands.She also explains the medical, legal, and insurance maze. In a time when almost 10 million Americans currently need long-term care, The Eldercare Handbook is an essential read.

Will to Live
¥99.65
In a survival situation, a wrong decision could spell the difference between life and death. No one knows this better than Les Stroud, who has survived everywhere from the sun-scorched sands of the Kalahari to the snake-infested jungles of the Amazon. In Will to Live, Les examines many incredible true life survival stories explaining what happened and why, and offering valuable perspectives on what went right, what went wrong, and what could have been done differently. The tales in Will to Live include: Chris McCandless the subject of the book and movie Into the Wild. Yossi Ghinsberg who survived alone in the Amazon for twenty-one days. Douglas Mawson the Antarctic "superman" who survived three hellish months at the bottom of the planet. Nando Parrado who was trapped for two months high in the Andes after a plane crash killed his friends and family. Plus . . . stories from Les's own experiences, along with practical sidebars with tips on how to escape quicksand, butcher a moose, cross a snow-covered crevasse, and more. Provocative and entertaining, Will to Live is a compilation of history's most intriguing survival stories from one of the world's foremost experts.

Like Dreamers
¥101.00
In June 1967, Israel achieved the unimaginable a decisive victory against Egypt, Jordan, and Syria in the Six-Day War. The most symbolic triumph for the young nation was the reunification of Israeli West Jerusalem and Jordanian East Jerusalem, achieved at great cost by a group of paratroopers from the 55th Paratroopers Reserve Brigade. In restoring Jewish sovereignty to the Holy City, these men fulfilled the dream of two millennia, changing the history of Israel and of the Middle East. And as veteran journalist Yossi Klein Halevi shows in Like Dreamers, they played pivotal roles in shaping Israel's destiny long after their resounding military success.A masterful storyteller, Halevi tracks down seven members of the 55th Brigade and traces their lives through the decades following the Six-Day War. But as his narrative reveals, despite the intensity of their shared experience protecting Israel, in their postwar paths they nurture drastically divergent visions for the country's future. Yoel Bin-Nun emerges at the forefront of the religious Zionist West Bank settlement movement, but Arik Achmon the chief intelligence officer of the 55th becomes a spiritual father of the unilateral withdrawal from Gaza in 2005. Achmon becomes a driving force in the growth of Israel's capitalist economy, whereas Avital Geva, in addition to building a reputation as a leading conceptual artist, ardently defends the socialist kibbutzim. And while Geva is among the foremost activists in Peace Now, Udi Adiv helps create an anti-Zionist terror underground in Damascus, eventually serving twelve years in an Israeli prison.Charting the ideological differences among this band of brothers, Halevi weaves a nuanced and insightful chronicle of modern Israel. His fascinating, diligently researched examination of each man's motivations and actions supported by extensive interviews with their friends, family members, and comrades-in-arms humanizes the country 's complex political landscape, facilitating a deeper understanding of the forces that influence its evolution as a state.
Finders Keepers
¥35.01
More than anything in the world, Molly Eden wants a child and then one day she finds one in her backyard! But this is no abandoned toddler. A man has followed the mischievous boy onto her property, a concerned father whose rugged good looks take Molly's breath away, while the sadness about him tears at her heart.Joseph Rossi never expected to find his tiny son running into the arms of an unknown woman, but Joey craves a mommy and it seems he's chosen one and Joseph approves of his choice. What chance could a single father possibly have with an enchanting free spirit as sweet and sexy as Molly Eden, who must have a hundred men clamoring for her attentionStill, he knows in his heart what Joey knows: that Molly is the one. Now he must prove it to her and show Molly a man who is more than just a daddy but also a tender and passionate lover...and, perhaps, the perfect husband.
Your Scandalous Ways
¥48.91
James Cordier is all blue blood and entirely dangerous. He's a master of disguise, a brilliant thief, a first-class lover all for King and Country and, by gad, he's so weary of it. His last mission is to "acquire" a packet of incriminating letters from one notorious woman. Then he can return to London and meet sweet-natured heiresses not adventuresses and fallen women.Francesca Bonnard has weathered heartbreak, scorn, and scandal. She's independent, happy, and definitely fallen; and she's learned that "gentlemen" are more trouble than they're worth. She can also see that her wildly attractive new neighbor is bad news.But as bad as James is, there are others far worse also searching for Francesca's letters. And suddenly nothing is simple especially the nearly incendiary chemistry between the two most jaded, sinful souls in Europe. And just as suddenly, risking everything may be worth the prize.
Freedom
¥88.56
There are few men who are as quintessentially American as Sonny Barger. He is patriotic a veteran who loves his country. He is independent choosing his own path on his motorcycle, living life on his own terms. He is outspoken he has boldly criticized injustices in American law and society despite the backlash this has evoked from the establishment. Yet the element that he finds most important, most sacred, most American, is freedom.In Freedom, Sonny articulates many of the principles he employs in his own life. Whether he is regarded as a leader, a rebel, a revolutionary, a criminal, or a soldier, Sonny's outlook has been influenced not just by school but by the military, prison, and his experiences riding with the world's most notorious motorcycle club. It was on these various journeys that he learned the lessons that are most important in his life and the qualities he respects when he sees them in others:IndependenceCustomize Yourself; Originals Don't Come Off an Assembly LineToughnessTemper the Steel to Forge a Strong BladeFairness Treat Me Good, I'll Treat You Better; Treat Me Bad, I'll Treat You Worse Presented in the form of fifty credos, this book gives Sonny Barger's perspective on how to live a life that embodies the most fundamental of American virtues: freedom.
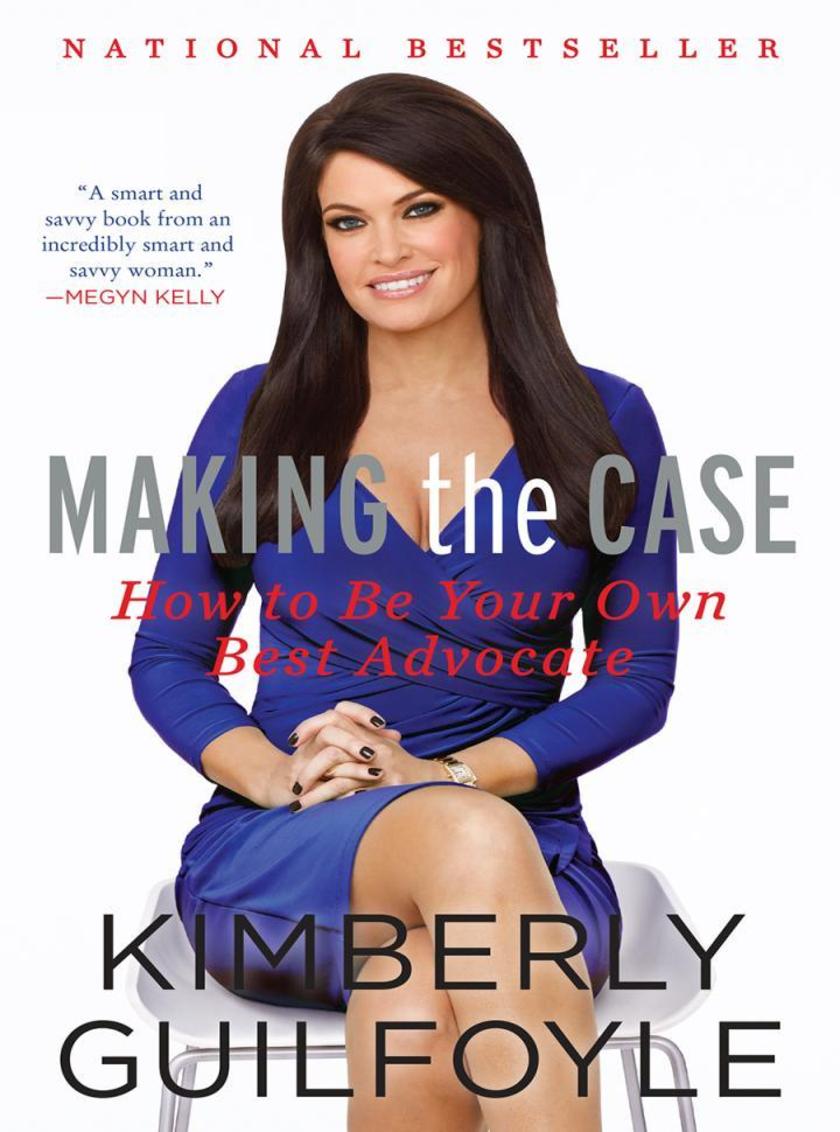
Making the Case
¥88.56
After an eleven-year-old Kimberly Guilfoyle lost her mother to leukemia, her dad wanted her to become as resilient and self-empowered as she could be. He wisely taught her to build a solid case for the things she wanted. Creating a strong logical argument was the best way to ensure she could always meet her needs. That childhood lesson led her to become the fearless advocate and quick-thinking spitfire she is today. In Making the Case, Guilfoyle interweaves stories and anecdotes from her life and career with practical advice that can help you win arguments, get what you want, help others along the way, and come out ahead in any situation.Learning how to state your case effectively is not just important for lawyers it's something every person should know how to do, no matter what stage of life they are in. From landing her dream job right out of school, switching careers seamlessly midstream, and managing personal finances for greater growth and stability to divorcing amicably and teaching her young child to advocate for himself, Guilfoyle has been there and done it. Now she shares those stories, showing you how to organize your thoughts and plans, have meaningful discussions with the people around you, and achieve your goals in all aspects of your life. You'll also learn the tips and strategies that make the best advocates so successful, some of which come directly from courtroom scenarios where the stakes are highest.Told in her winning and humorous voice, Guilfoyle's experiences and the wisdom drawn from them are a ready guide to help you reach your potential and live a fulfilling and happy life at work and at home.
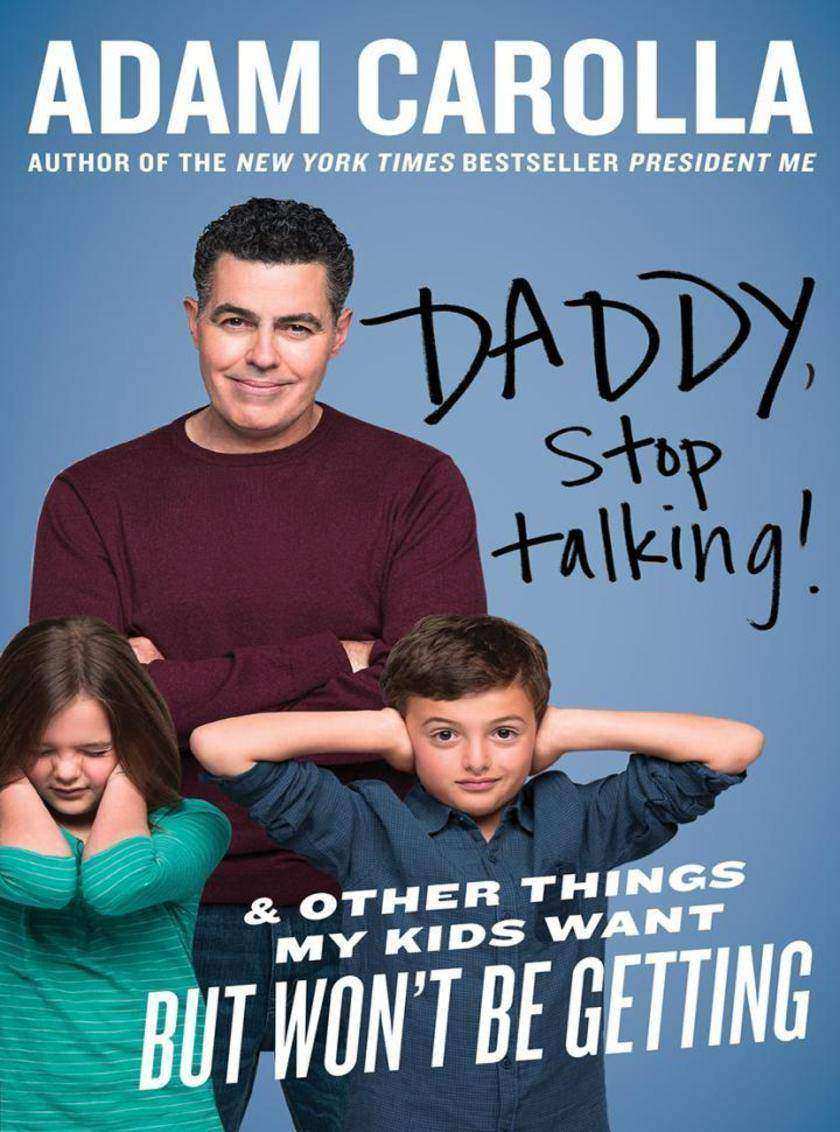
Daddy, Stop Talking!
¥94.10
Last Will & Testament of Adam CarollaI, Adam Carolla, being of beaten-down mind, declare this to be my Last Will and Testament. I revoke all wills and addendums previously made by me. (You guys never did listen, anyway.) Article II appoint the rest of the world's unappreciated dads as Personal Representatives to administer this Will. I bequeath to them the right to crack a couple cold ones in the garage after working their asses off all week and ask that they be permitted to watch all the porn they like and not have to change diapers and get dragged to every preschool "graduation" and PTA meeting. Article IITo my wife, I leave a safe-deposit box, the sole content of which is a note reading "Get a job. I'm dead," and my best wishes on trying to keep up with the unending demands of our houses, cars, dog, and kids.Article IIII devise, bequeath, and give my kids this book, Daddy, Stop Talking. Since you guys were the death of me, I leave you these pages of wisdom. But no cash, cars, or property. You've got to earn those. On that note, I further demand that the following message be placed on the marker of my grave: "You're All on Your Own Now. Enjoy."
One More Step
¥95.39
In 2008, Bonner Paddock summited 19,341-foot-high mount kilimanjaro, the world's tallest freestanding mountain. Four years later, he earned the elite triathlete title kona Ironman. Thousands have done each individually. Bonner is the first person with cerebral palsy to do both.Bonner Paddock grew up just wanting to be ordinary. Despite his skinny legs and habit of tripping over nothing, he fought to keep up with his athletic older brothers, learned to battle riptides with his grandfather on close watch, and did everything he could to feel like a regular kid, even when it became clear he wasn't. After being diagnosed with cerebral palsy at age eleven, Bonner didn't let it limit him instead he simply ignored its existence. For the next eighteen years, he guarded the truth about his health, building a normal life and keeping his secret from everyone most of all himself.But the sudden death of a friend's young son named Jake, a boy who also suffered from cerebral palsy, forced Bonner to reevaluate who he was. No longer content striving for normal, he began to pursue one breathtaking experience after another in Jake's memory, never hiding from his physical limitations and, in the process, raising international awareness about cerebral palsy. T is appetite for challenges led him to the foothills of Mount Kilimanjaro where, pushing his fragile body to the brink and barely surviving, he braved one mountain only to discover that he still had farther to climb.Embracing his weaknesses to understand his strengths, he then pursued the ultimate adventure: testing his mind, body, and will at the Ironman in Kona, Hawaii, a race regarded by many as the hardest on earth. Along the way he forged a renewed bond with his family and launched a foundation to help disabled children in Africa and at home.In the end, his remarkable journey took him across the globe and introduced him to a compelling cast of characters from Tanzanian mountain guides to top-class surgeons, to disabled children, to champion athletes all of whom inspired his quest. Infused with his irresistible charisma, courage, and heart, and illustrated with sixteen pages of color photos, One More Step is a gripping story of human perseverance that demonstrates how our lives are not defined by limits, but by the moments and lessons that push us past them.
The Storm of the Century
¥100.71
In this gripping narrative history, Al Roker from NBC’s Today and the Weather Channel vividly examines the deadliest natural disaster in American history—a haunting and inspiring tale of tragedy, heroism, and resilience that is full of lessons for today’s new age of extreme weather. On the afternoon of September 8, 1900, two-hundred-mile-per-hour winds and fifteen-foot waves slammed into Galveston, the booming port city on Texas’s Gulf Coast. By dawn the next day, the city that hours earlier had stood as a symbol of America’s growth and expansion was now gone. Shattered, grief-stricken survivors emerged to witness a level of destruction never before seen: Eight thousand corpses littered the streets and were buried under the massive wreckage. Rushing water had lifted buildings from their foundations, smashing them into pieces, while wind gusts had upended steel girders and trestles, driving them through house walls and into sidewalks. No race or class was spared its wrath. In less than twenty-four hours, a single storm had destroyed a major American metropolis—and awakened a nation to the terrifying power of nature. Blending an unforgettable cast of characters, accessible weather science, and deep historical research into a sweeping and dramatic narrative, The Storm of the Century brings this legendary hurricane and its aftermath into fresh focus. No other natural disaster has ever matched the havoc caused by the awesome mix of winds, rain, and flooding that devastated Galveston and shocked a young, optimistic nation on the cusp of modernity. Exploring the impact of the tragedy on a rising country’s confidence—the trauma of the loss and the determination of the response—Al Roker illuminates the United States’s character at the dawn of the “American Century,” while also underlining the fact that no matter how mighty they may become, all nations must respect the ferocious potential of our natural environment.
Motherpeace
¥110.71
For over a decade, Motherpeace has been an inspiration and oracle for women all over the world. Motherpeace recovers the positive, nurturing peace-oriented values of prepatriarchal times, and brilliantly combines art, history, mythology, folklore, philosophy, and comparative religion with an informed spiritual and feminist perspective.Vicki Noble challenges us to celebrate our ancient peaceful heritage and to reclaim our right as a people to a life without war. The book is a vision of hope and transformation, made even more powerful by the vibrant pictorial images of the seventy-eight Motherpeace tarot cards.Motherpeace shows how traditional myths and symbols can provide ideas and images for understanding the meaning and power of the Goddess for women and men today.
The Greatest Music Stories Never Told
¥112.23
Did you know about: The ballet that sparked a riot The rock star who became an astrophysicist The song that saved Wheaties The man killed by his own conducting The controversy behind "Mary Had a Little Lamb"Prepare to be astonished, bewildered, and stupefied by the tantalizing tidbits of music history collected here: amazing stories about jazz, classical, country, rock 'n' roll, hip-hop, show tunes, composers, band names, song lyrics, instruments, technology, controversies, and more. Learn how the FBI spent years trying to decode the lyrics of one rock song. Discover how Watergate provided the inspiration for A Chorus Line. Find out how one megahit was born in a history class, while another was dashed off in a fit of anger at actor Robert De Niro. Meet the monk behind solfège, the aviation pioneer who created Muzak, and the prisoner who literally sang himself out of jail. Then there's the most important person in rock 'n' roll history—chances are you've never heard of him! Continuing the successful Greatest Stories Never Told series, Rick Beyer has delivered another classic volume for history and music buffs alike.
What is Your Life's Work?
¥128.85
What Is Your Life's Workcaptures a most extraordinary moment in each of our lives the time when we sit down with loved ones and attempt to answer the big question about what really matters. Bill Jensen has created a wonderfully practical space for you to explore who you are, what you stand for, what you believe in, what's risky, what's not, what's worth it, what you're struggling with, and what you've accomplished.He has captured the intimate exchanges between mothers and daughters, fathers and sons, and caring teammates all talking about what really matters at work, and in life. Their conversations are as real as yours would be: "Don't kiss tush, beware carnivorous sheep." "Honey, there are no shortcuts." "My daughter was limp with pain ... and I'm worried about deadlines. What was I thinking?!?!" "Speak up if you don't agree." "Be a respectful rebel." In What Is Your Life's Workyou will discover a new way to see and know who you are in today's more-better-faster world. Exposed is what usually stays private; the raw truths we've all experienced, the personal frailties and mistakes we'd like to hide, and the proudest achievements we'd like to celebrate.In the letters and work diaries of others, we see ourselves. In their struggles, we see our own.Bill Jensen has made it his life's work to battle corporate stupidity and help us all simplify our workdays, take more control, and rediscover our passions. As your trail guide and partner, he will take you through five distinct discoveries that thousands have encountered in finding their voices: Finding Yourself Finding the Lessons to Be Learned,the Questions to Be Asked Finding the Choices That Really Matter Finding the Courage to Choose Finding Joy, Serenity, and FulfillmentWhile it touches your heart and lifts your soul, What Is Your Life's Workdoes not shy away from difficult introspection. You are an active participant in this book. Yes, you will find value here stories of people like you, new ways of looking at what really matters, or simple confirmation that others have chosen the same path as you.But the ultimate takeaway asks something of you in return: Take something from this book and pay it forward. Start a new conversation with a loved one about what really matters about your own life's work.You will get back even more than you give. You will have brought these pages to life.




 购物车
购物车 个人中心
个人中心



